If information security and data protection incidents happen, make sure that they are reported and managed effectively across your entire organisation. By creating a clear process in the Granite Information Security and Data Protection Incidents tool, your teams can report, handle and implement corrective actions with an easy workflow and clear reporting.
These incidents occur when an organisation’s security or data protection standards or regulations are violated, leading to data-related risks or breaches. Managing these incidents is a crucial part of developing and maintaining your organisation’s information security. Granite’s incident management processes support you in meeting data protection guidelines and demonstrating compliance, reducing security risks and improving data protection as a whole.
The Granite Information Security and Data Protection Incidents tool is designed to support organisations in managing security and data protection risks.
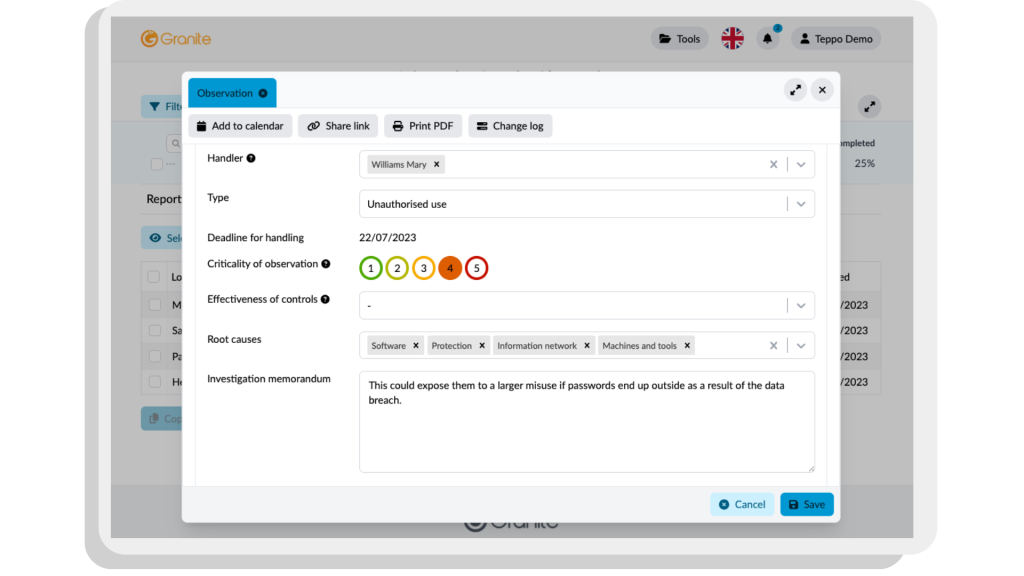
This tool allows low-threshold reporting of incidents, document handling and implementation of corrective actions.
With the authority guidelines and compliance at the heart of Granite’s platform, the tool can help you enhance security levels, manage risks and ensure business continuity in all situations.
The Granite Information Security and Data Protection Incidents tool empowers you to effectively manage any incident that is thrown at you. The tool is designed to allow your entire organisation to participate in improving security culture, by ensuring that problems are handled correctly and quickly.

Empower your entire staff to easily and quickly report information security and data protection incidents.

Gather information on security improvements areas, assess the impact of incidents and manage all of your risks proactively.
Establish your organisation's security level and threats to make sure business continuity is paramount whatever the circumstances.
Systematically manage and document all incidents and near-misses, making sure to constantly improve your processes.
Document incident handling, investigation, and corrective actions, ensuring transparency and evidence-based decision-making.

Gain maximum insights from Granite’s tool, when you include security risk management with smooth execution of audit plans.
Ask us for a demo or let us chat about your needs.